Improve Your Enterprise Mobile Security with Constant Visibility
Network security is quite simple when you know what you are dealing with. In a standard desktop/laptop setup, you can easily monitor all network traffic and determine if a rogue element is present.
The reason this is possible is that every computer is connected to the same network, and all data has to pass through a server, firewall, or router at some point on its journey.
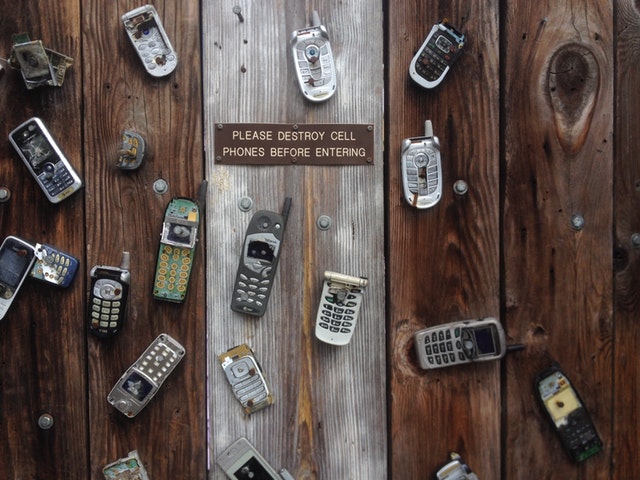
Unfortunately, this kind of constant visibility is not the default configuration for networks with a mobile element. It can be difficult to track what information a device is sending out or receiving if it is working over a cellular network. (1)
Other Networks Bring New Problems
Many businesses do not have policies or rules in place for what happens when a device connects to a network that is not the corporate Wi-Fi network. (2) With BYOD becoming increasingly common, it stands to reason that devices may connect to multiple networks.
Within the corporate setting, all data can be routed through firewalls or filtered in other ways. Once the device connects to another network, these rules simply cannot apply – the firewall and filtering doesn’t exist.
Any server can be connected to, any data sent or received. And while in many cases this is safe, if opens a world of opportunities for those who may wish to cause problems, such as hackers and writers of malware.
Improving Visibility With Management
Using the appropriate mobility management software will allow tech teams to monitor the network activity on mobile devices no matter what path it takes to send or receive it. In fact, it is possible to manage and monitor devices fully, preventing unauthorized access and blocking possible hacking attempts or malware.
The first step to combating these problems is simply visibility – it is hard to defend against something you cannot see and are not aware of. (3) The biggest problem facing businesses today if discovering these problems, rather than fighting against them.
With correctly configured software and devices, the corporate and personal sides of the equation can be kept completely separate. There can be no data leakage, no hacking into trade secrets, and no problem for the business.
While software to perform these tasks is easily available, configuring it is not always straightforward. The best way to ensure that every switch is selected, and all the right boxes are checked is to use a Mobility Lifecycle Management company, skilled and experienced in all aspects of mobility management.
It is certainly worth relying on the knowledge of a dedicated company than it is to work blind and try to figure it all out by yourself.
References